Connectivity – at the heart of Collaborative Combat

Can we replicate human intuition with technology? If intuition is a matter of the human brain ‘joining the dots’ from all its data collecting senses and mixing them with a lifetime of experience and knowledge then connectivity is the term we might give to the technical approach. In the military environment ‘connecting the dots’ or connectivity lies at the heart of what we call ‘Collaborative Combat’ and the capability which allows the decision maker to ‘See the Unseen’.
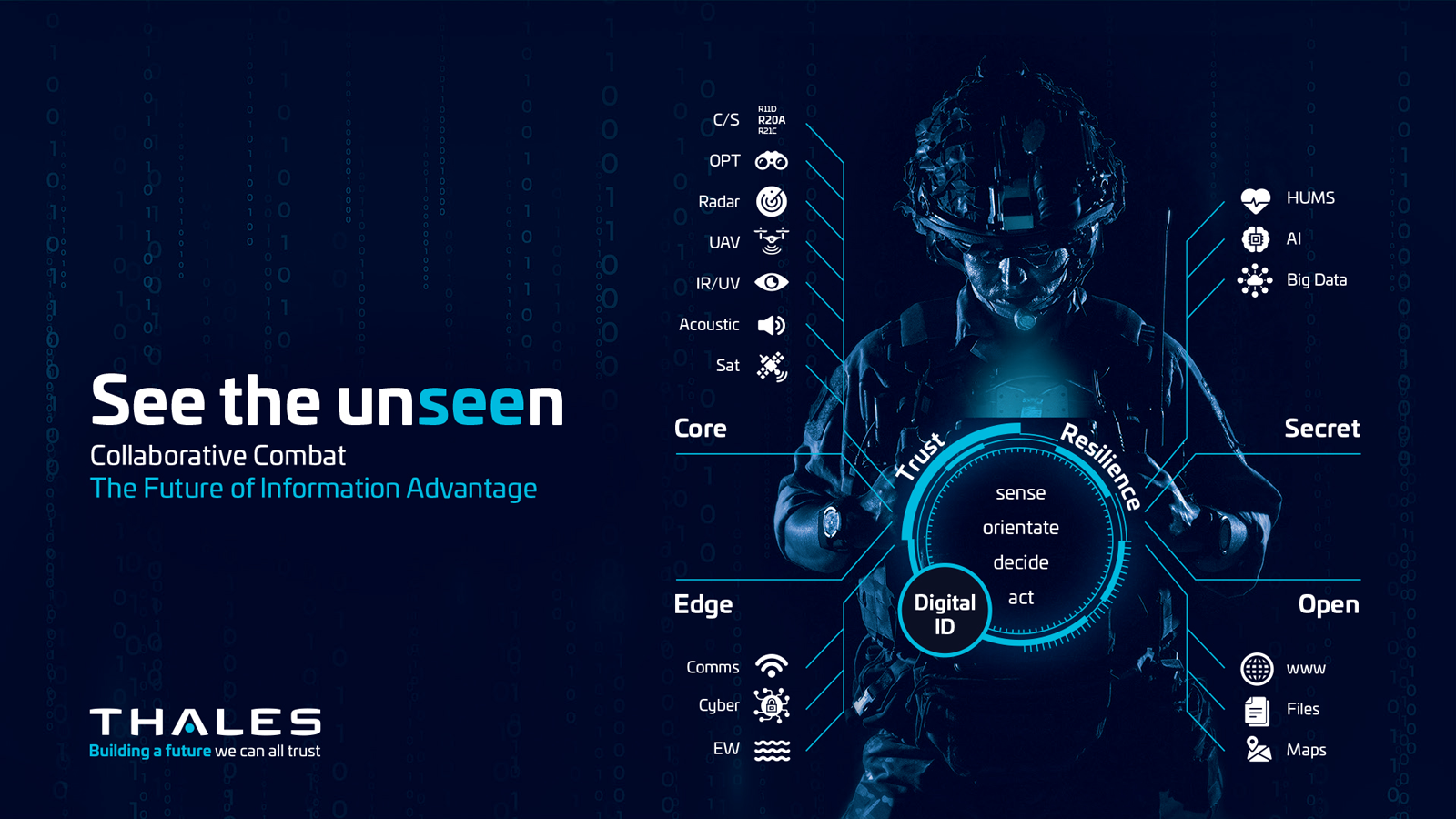
Today, across the ‘battle space’ there are sensors that collect data, bearers that move data, and software that can sort, join up, and categorise the data. There is even AI that can process volumes of data at speeds which remove the need for manual application of human intelligence to process information, or apply algorithms which provide new means for visualising and manipulating data and which draw can the user’s attentions to priority information requirements, novel threat vectors or other user centred intelligence opportunities. By bringing it all together we believe that we can create a new ‘digital intuition’ allowing commanders and decision makers to ‘see the unseen’ but it requires a completely integrated approach from sensor to decision maker (software or human) over secure bearers, with secure and controlled access. It also requires vision – both for unity of purpose and for ability to deliver.
Today, as militaries transform, and geopolitics alter how we see effect delivered we understand that the military end user aspires to:
- deploy at small or large scale independently or with allies
- work across a variety of benign and harsh environments
- be interoperable with armed forces and civilian agencies
- be protected from the most likely cyber threats
This, in turn, drives C4I design to:
- be highly modular and secure by design
- be uncompromisingly user friendly to train on and to fight with
- be fully interoperable with other nations in a highly dynamic operational setting
Which means that manufacturers therefore seek to address the following data challenges:
- Numbers of sensors on the battlefield will increase with the development and deployment of each new sensor-effector capability
- Data consumption will continue to grow exponentially over the next decade, generating and storing immense masses of data every moment of every day
- Making sense of mass data and protecting meta-data will bring a range of military benefits but also myriad critical challenges.

One way to address these challenges is to envisage a battlefield observed, or rather understood, with digital intuition. Imagine the senses are things like digital cameras, sights, acoustic sensors, and radars on myriad platforms, whether for aiding drivers or providing gunners with targets, all feeding in imagery from across the environment. Edge processing (software embedded in the sensor itself, with its own computing capacity, able to operate whether connected to the defence cloud or when comms are denied) augmenting the capability and deciding which data is important to pass on; terrain profiles, image recognition, anomaly detection, the action of processing reducing the actual amount of data being passed over crowded connectivity bearers. The User experiences very similar effects to when connected to different commercial devices, with high end services and richer data streams at one end of the C4ISR performance spectrum and more basic functions dependent when the level of connectivity or compute power is reduced.
Of course the vision for such interconnectedness between sensor and shooter is not new. Third party designation, fire and forget, networked enabled capability has all been pre-figured since the advent of laser guided weapons and satellite communications going back to the 1960s. What is perhaps different now is the availability of existing technologies due to miniaturisation and the need to solve bandwidth and data capacity constraint challenges (we might call this the technological means) together with the military necessity or programmatic possibility to realise the vision (we might call this the operational motivation), then the conditions to transform C4ISR on the battlefield is being addressed. When the whole of a defence organisation buys into the technical means and the operational motivation to improve joint effects, then the likelihood of achieving multi-domain integration aims is much improved.
Increased Multi-Domain Integration would mean that the data from air and naval assets; IR sensors on aircraft, EW assets on ships, satellite observation and cyber surveillance could also add to a near complete picture of the conflict environment. Today vast amounts of data are available from a dizzying array of sources and sensors creating unbelievable amounts of data.
All of these ‘digital senses’ can be connected across the battlefield via software defined and fully encrypted radios, ensuring the safe delivery and complete trust of the data delivered to a ‘Defence Cloud’ where data, cross domain, can be collated, analysed, processed and shared.
Having a trusted common operating picture, one which allows widely dispersed commanders and operators to access data seamlessly, at the tactical edge, with computational capability whether connected to a cloud or in a comms denied location, or whether embedded in a headquarters, or mounted on the move. This is information advantage.
But the more connected and open systems become, the tougher it is to be sure they’re not vulnerable to attack. Networks and bearers that deliver data resilience to remote users in the field, secure from cyber-attack in the home-base is also key to information advantage. Clearly, full integration will only be achieved if we can be confident that our systems are completely secure.
At the moment, much military security still relies on separation, the strict control of connection, and the protection of perimeter. This is a bit like strengthening castle walls and changing all the locks to keep people out – but then having to let some of them in through the back door to re-stock the larder or fix the electrics, and not being entirely sure you can trust them.
The civilian world overcomes this by taking a much more data-centric view: it renders data indecipherable at rest or on the move, except to those who are trusted to use it. This means that the heart of effective security is the trusted user. This means identity verification is the foundation of the secure system.
Think of logging on to your bank via your phone: your bank wants to be absolutely sure it’s you before releasing a one-time unbreakable code that allows me to conduct my transaction. And when you log out (or if you’re inactive for a certain amount of time) all trace of the session and any account or security details are erased.
This is made possible because each person carries with them a number of unique identifiers – a personal digital identity, whether it is fingerprints, facial recognition or some other personal key. The more we can integrate biometry-related cross-checking of identity into military networks, the more we will be able to open up military networks and interfaces, establishing the digital trust necessary to transform information advantage of the whole force.
This is how Thales believes the future battle space will work; dispersed sensors, sometimes operating autonomously, providing data and information into a central and ubiquitous shared cloud, providing information advantage and systemic protection through mutual support, to deployed forces in areas of conflict. We see an opportunity to use technology to create digital intuition allowing decision makers to ‘see the unseen’?
We believe this because this is what we deliver. Across the spectrum of the Land Defence domain and beyond through multi-domain integration, Thales offer capability across all of these sensors, bearers, processing and software, with experience in delivering complex systems of systems, bringing the most advance technological solutions to our customers in both the civil and defence markets helping them address the problems they face and move towards the future they desire.