Digital transformation – Protect. Monitor. Change behaviour.
Gareth Williams, on the essentials for staying safe on your journey to Industry 4.0
Everyone wants the benefits of Industry 4.0. But before you launch into connecting everything up, old and new, you need to understand – really understand – the equipment that’s critically important to your business. Then you need to:
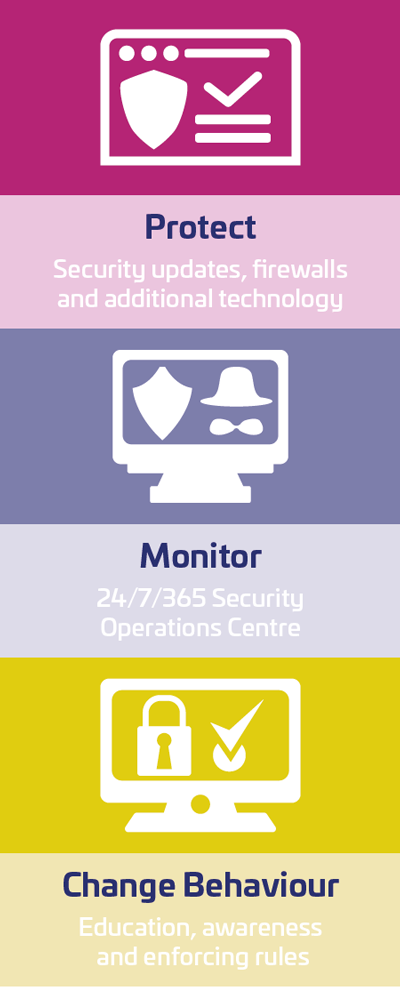
- Protect: mission-critical equipment can often be protected by installing the latest security updates, reconfiguring firewalls or deploying additional technology. This a relatively straightforward but important first step, which you can probably manage in-house.
- Monitor: some of your plant might be impossible to fully protect, too hard to change and prohibitively expensive to replace or re-engineer. That’s when you need to adopt a monitoring stance. The simplest way is to hire a third-party Security Operations Centre to keep a 24/7 vigil on your Operational Technology and Information Technology. When it sees an attack in progress it will shut that system down (if necessary), nullify the problem and then bring it back online as quickly and smoothly as possible.
- Change behaviour: most cyber incursions are made possible by human error or negligence. You can make huge improvements to the security of your Operational Technology and Information Technology through education, building awareness and enforcing rules. Everyone shares the responsibility to safeguard your systems.
Not long ago, one of my teams was visiting a factory in Turkey when an attack started happening. A swift investigation revealed that an engineer was loading a file on to an old and unprotected machinery. Because the file was too large he decided to use SharePoint. He loaded the file all right, but someone took advantage of SharePoint to introduce the WannaCry virus (the same as that which inflicted £92 million of damage to the UK’s National Health Service in 2018). It wasn’t a good day.
Digital trust: the foundation of Industry 4.0
After Protect, Monitor, and Change Behaviour, you’re ready to start planning a move towards connecting to your supply chain and other third parties. That opens up a whole new set of risks and unknown threats. So before you start sharing data and granting access to your networks, you've got to think about security all over again.
Is the user who he appears to be? Can you trust the source and content of the data? How do you control who is allowed to see what? If a trusted member of your digital ecosystem suffers an attack, can you isolate that part of the system and carry on? Has that attack put you or other members of the supply chain at risk? What about the firms which supply your suppliers: do they need to be in your digital ecosystem? Have they already been compromised? How do you know?
Established security technology such as Public Key Infrastructure and blockchain will resolve a lot of these questions, but they need an implementation which is appropriate for your particular industry and tailored to your unique digital ecosystem. You’ll probably need a few additional services, too, to bring everything together, beefing up robustness and resilience.
Getting ready. Staying safe.
Make no mistake, this is a massive undertaking. But it can be done – safely, on time and within budget – if you team up with a partner that is familiar with your industry and your operational technology, and is experienced in creating digital trust. Investigate patiently. Choose wisely.
The world is getting ready to move to Industry 4.0. For some, the journey has already started. Your success will depend on taking operational technology as seriously as information technology, and by finding technology partners have the skills and resources to get you there.
More News




